#digital equipment corporation
Text

VAX 7000
#dec#vax#digital#retrocomputer#retro#retrocomputing#big iron#mainframe#digital equipment corporation#vax 7000#big computer
173 notes
·
View notes
Photo
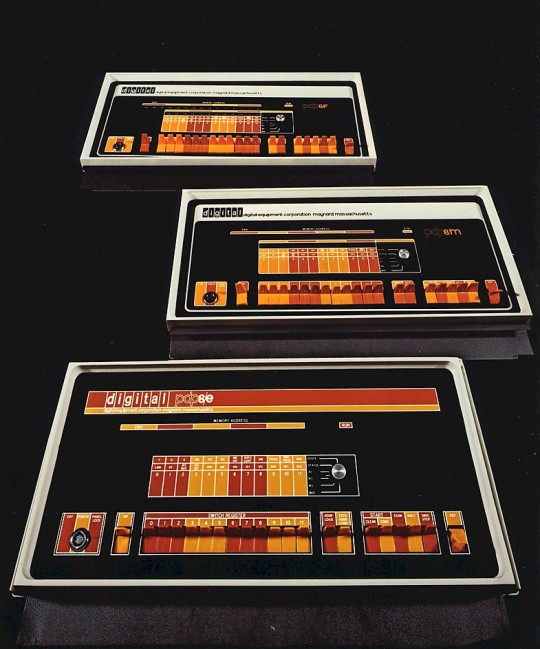
Digital Equipment Corporation PDP-8/E, /F, and /M, 1972.
665 notes
·
View notes
Text

When I worked for DEC, I used to love reading the internal DECNotes message board that had collected stories from Field Service about weird installations of our computers.
By far the best one concerned a PDP 11/73, like the one above, that was used to measure nuclear bomb yield. The story went that the system was in a shaft leading to the underground test chamber, and it took readings on the explosion in real time until it was vaporized.
I always hoped this was true but took it with a grain of salt - but this archive.org post about just such a setup at Los Alamos backs it up. The test method is quite ingenious too - the system uses time domain relfectometry (TDR) measurements to measure a length of cable between the bomb and the computer. As the bomb explodes, the blast eats away at the cable, and they can figure out yield and stuff based on how fast it happens.
The PDP 11 is indeed not spared in the process, it transmits its results to a distant receiver before being destroyed what can only be at most seconds later.
That's why the instructions are clear to say "start with a PDP 11 you no longer love." lol.
188 notes
·
View notes
Text

Digital Equipment Corporation DECMate II
Large Scale Systems Museum (LSSM) - mact.io - Pittsburgh, PA
488 notes
·
View notes
Text

#dec vt220#vt220#digital equipment corporation#objectum#GAH THEY ARE SO PRETTY#I WANNA MAKE A GUSHING POST SO BAD BUT IM A BIT SHY ABT IT#BUT BASICALLY OH MY GOSH THE WAY IT HAS THREE DIFFERENT COLORS#like all three colors looks good on it amber green and blue#beautiful machine
28 notes
·
View notes
Photo

DEC VT100 (1978)
36 notes
·
View notes
Text
youtube
DECtalk Flexidisc Demo 1984
#dectalk#speech synthesis#text to speech#flexi disc#dec#eva-tone#soundsheet#video#fran blanche#1984#digital equipment corporation#flexidisc#ephemera#youtube
1 note
·
View note
Text
It's been many years since I first read the (fictional) story linked above. Today I got an urge to revisit it. I was glad to find it online without much difficulty.
I should explain that a VAX was a computer about the size of a refrigerator. Perhaps by analogy with "ox", the English plural of VAX was VAXen.
VAXen were manufactured by Digital Equipment Corporation (DEC) from 1977 to 1990 or so. They had nothing to do with vaccines---or the "Critical Role" webseries.
In those days, serious computing work (such as weather forecasting and air-traffic control) took place on mainframe computers such as the IBM 3090. A single 3090 could fill a room. Imagine rows of cabinets, reel-to-reel tape drives, fluorescent lighting, raised flooring, and deafening fans. Maintaining a single 3090 provided employment for a department.
VAXen, by contrast, were classified as minicomputers. Due to their relatively low cost-of-ownership, they invaded corporate datacenters during the 1980s, leading to some epic geek-on-geek culture clashes. And so our story begins...
#war stories#information technology#operating systems#reboot#programmer humor#mainframe#ibm#geek culture#taxonomy#digital equipment corporation
0 notes
Text
Orlando Video Production | Full Video Production Services
Business Video Solutions is Orlando’s Video production company that promotes your products and sercives with their professional videograpgy services.
#Business Video Production Services#Video Solutions#Video Production Company#Video Producing Companies#Corporate Video Solution#Corporate Video Production Services#Professional Video Production Company#Digital Video Production Companies#Video Production Services#Full Service Video Production#Full Video Production Services#Marketing Video Services#Production Studios In Orlando#Orlando Video Production Companies#Video Company Orlando#Video Production Company Orlando#Orlando Video Production Company#Orlando Video Production#Camera Lens Rental#Camera Equipment Rental#Production Company Orlando#Video Production Company in Orlando#Video Production Services Tampa#Best Video Solutions#Business Video#Businesses Video#Videosolutions#Video Business
0 notes
Text
John Deere's repair fake-out

Last week, a seeming miracle came to pass: John Deere, the Big Ag monopolist that — along with Apple — has led the Axis of Evil that killed, delayed and sabotaged dozens of Right to Repair laws, sued for peace, announcing a Memorandum of Understanding with the American Farm Bureau Federation to make it easier for farmers to fix their own tractors:
https://www.fb.org/files/AFBF_John_Deere_MOU.pdf
This is a move that’s both badly needed and long overdue. Deere abuses copyright law to force farmers to pay for official repairs — even when the farmer does the repair. That’s possible thanks to a practice called VIN locking, in which engine parts come with DRM that prevents the tractor from recognizing them until they pay hundreds of dollars for a John Deere technician to come to their farm and type an unlock code into the tractor’s console:
https://doctorow.medium.com/about-those-kill-switched-ukrainian-tractors-bc93f471b9c8
Like all DRM, VIN locks are covered by Section 1201 of the Digital Millennium Copyright Act (DMCA), a 1998 law that criminalizes distributing tools to bypass “access controls,” even if you do so for a lawful purpose (say, to fix your own tractor using a part you paid for). Violations of DMCA 1201 carry a penalty of 5 years in prison and a $500k fine — for a first offense.
This means that Deere owners are locked into using Deere for repairs, which also means that if Deere decides something isn’t broken, a farmer can’t get it fixed. This is very bad news indeed, because John Deere tractors are just computers in a fancy, mobile case, and John Deere is incredibly bad at digital security:
https://pluralistic.net/2021/04/23/reputation-laundry/#deere-john
That’s scary stuff, because John Deere is a monopolist, and a successful attack on the always-connected, networked tractors and other equipment it supplies to the world’s farmers could endanger the global food supply.
Deere doesn’t want to make insecure tractors, but it also doesn’t want to be embarrassed by security researchers who point out that its security is defective. Because security researchers have to bypass Deere tractors’ locks to probe their security, Deere can leverage DMCA1201 into a veto over who gets to warn the public about the mistakes it made.
It’s not just security researchers that Deere gets to gag: the company uses its repair monopoly to threaten farmers who complain about its business practices, holding their million-dollar farm equipment hostage to their silence:
https://pluralistic.net/2022/05/31/dealers-choice/#be-a-shame-if-something-were-to-happen-to-it
This all adds up to what Jay Freeman calls “felony contempt of business model,” an abuse of copyright law that allows a monopolistic corporation to reach beyond its own walls and impose its will on it customers, critics and competitors:
https://locusmag.com/2020/09/cory-doctorow-ip/
If Deere was finally suing for peace in the Repair Wars, well, that was wonderful news indeed — as I said, a seeming miracle.
But — like all miracles — it was too good to be true.
The MOU that Deere and the Farm Bureau signed is full of poison pills, gotchas, fine-print and mendacity, as Lauren Goode documents in her Wired article, “Right-to-Repair Advocates Question John Deere’s New Promises”:
https://www.wired.com/story/right-to-repair-advocates-question-john-deeres-new-promises/
For starters, the MOU makes the Farm Bureau promise to end its advocacy for state Right to Repair bills, which would create a repair system governed by democratically accountable laws, not corporate fiat. Clearly, Deere has seen the writing on the wall, after the passage in 2002 of Right to Repair laws in New York and Colorado:
https://www.eff.org/deeplinks/2022/06/when-drm-comes-your-wheelchair
These two bills broke the corporate anti-repair coalition’s winning streak, which saw dozens of state R2R bills defeated:
https://pluralistic.net/2021/05/26/nixing-the-fix/#r2r
Deere’s deal-with-the-devil is a cynical ploy to brake R2R’s momentum and ensure that any repairs are carried out on Deere’s terms. Now, about those terms…
Deere’s deal offers independent repair shops access to diagnostic tools and parts “on fair and reasonable terms,” a murky phrase that can mean whatever Deere decides it means. Crucially, the deal is silent on whether Deere will supply the tools needed to activate VIN locks, meaning that farmers will still be at Deere’s mercy when they effect their own repairs.
What’s more, the deal itself isn’t legally binding, and Deere can cancel it at any time. Once you dig past the headline, the Deere’s Damascene conversion to repair advocacy starts to look awfully superficial — and deceptive.
One person who wasn’t fooled is sick.codes, the hacker who has done the most important work on reverse-engineering Deere’s computer systems, culminating in last summer’s live, on-stage hack of a John Deere tractor at Defcon:
https://pluralistic.net/2022/08/15/deere-in-headlights/#doh-a-deere
Shortly after the announcement, Sick.codes tweeted how the fine-print in the MOU would have prevented him from doing the work he’s already done (including “a direct stab at me lol”):
https://twitter.com/sickcodes/status/1612484935495057409
As with other instances of monopolistic, corporate copyfraud — like, say, the deceptive Open Gaming License — the John Deere capitulation is really a bid to take away your rights, dressed up as a gift of more rights:
https://mostlysignssomeportents.tumblr.com/post/706163316598407168/good-riddance-to-the-open-gaming-license
[Image ID: Hieronymus Bosch's painting, 'The Conjurer.' The Conjuror's shell-game table holds a small John Deere tractor that the audience of yokels gawps at. One yokel is wearing a John Deere hat. The conjurer is holding a wrench.]
1K notes
·
View notes
Text
During the 80s DEC produced the Rigel chipset to power VAX workstations. The microprocessor code-named Rex had its own logo: a t-rex driving a convertible 🦖
#VAX#digital#dec#digital equipment corporation#microchip#retro#1980s#80s#retro computers#workstation#retrocomputer#t rex#dinosaur
33 notes
·
View notes
Photo

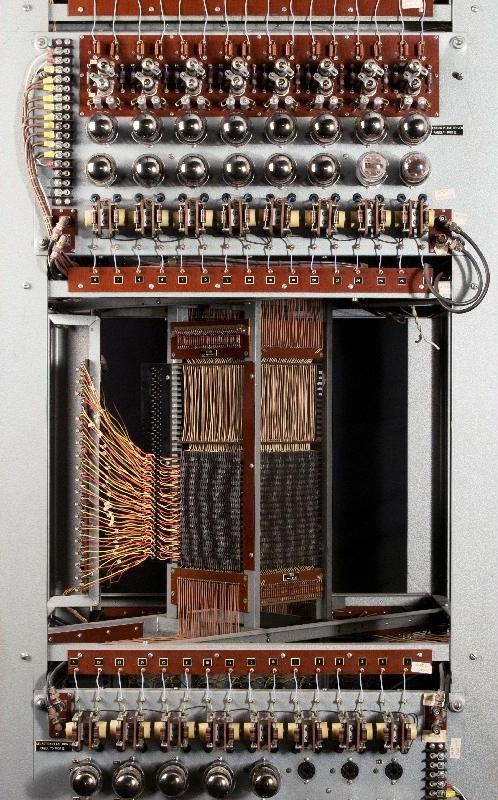
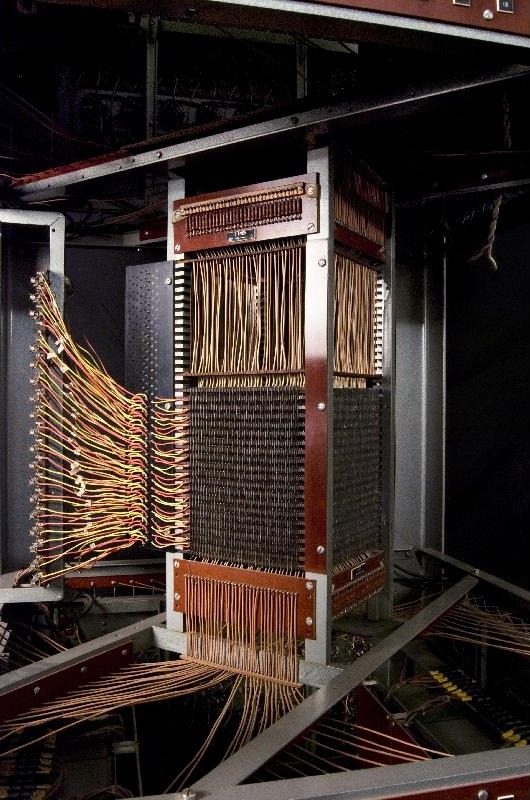

Core Memory Unit, Whirlwind Digital Computer, c. 1950
Digital Equipment Corporation Museum Collection
Massachusetts Institute of Technology, Cambridge, Massachusetts
image credits: MIT Museum
2K notes
·
View notes
Text

Found cleaning. Regrettably, Digital ran out of things for me to do in 1997.
76 notes
·
View notes
Text
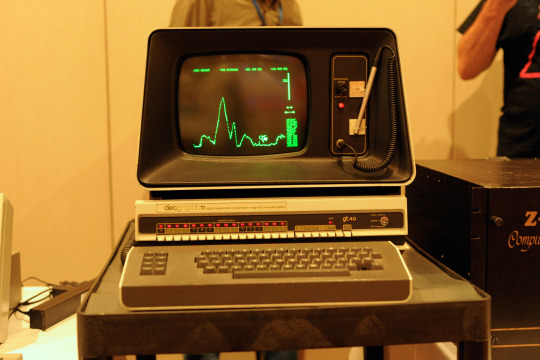
decgraphic11 aka the GT40, a specialized Digital Equipment Corporation PDP-11 - VCF Midwest 18
#vcfmw18#vcf midwest 18#vintage computer festival midwest 18#commodorez goes to vcfmw18#pdp-11#gt40#digital equipment corporation#DEC
74 notes
·
View notes
Text
Princess Anne’s speech at the Global Fraud Summit at the Guildhall in London on 10th March 2024.
“Digital IT is entirely global and so are fraudsters, they are globally organised and our response needs to be too.
The numbers of you here for the next couple of days, I hope affect the knowledge of the profound and far reaching impacts of fraud on ordinary people and that’s ordinary people everywhere in the world, particularly those who are least equipped to defend themselves.
Now in this conveniently, digital world, fraud of course, its impact go beyond individuals. It also undermines the foundations of trust and integrity that all our society are built on and it erodes confidence in the institutions. It tarnishes the reputation of businesses of any size and it shows the seeds of doubt amongst our citizens about how they proceed with businesses.
Fraud comes in many guises from that very personal impact to corporate fraud and governments and private organisations alike have a duty to protect citizens against fraud, but that requires concerted, collaborative effort from government, the private sector and civil society.
This global summit shows that this joint effort has already begun and many of you know each other and you know the organisations and some of you’ve got slightly different approaches. All of that is really important to the summit.
This is not a simple challenge but must not lose sight of the human toll that fraud exacts on ordinary people and Upholding the principles of trust and integrity and accountability that lie at the heart of our shared values, and if we don’t do that, I’m afraid it’s back to bartering and cash.”
56 notes
·
View notes
